sexta-feira, 30 de junho de 2023
<> SEO Max to improve ranks in 30 days <>
Get a powerful SEO Boost with our all in one SEO MAX Package and beat your
competition within just 1 month
Whitehat SEO plan, check out more details here
https://www.creative-digital.co/product/seo-max-package/
thanks and regards
Creative Digital
Unsubscribe:
https://mgdots.co/unsubscribe/
segunda-feira, 5 de junho de 2023
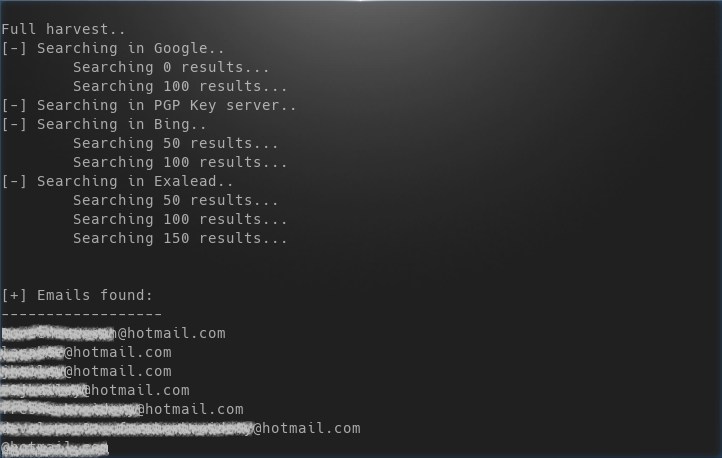
Theharvester: Email Harvesting Throughout Year
You might have harvested many things upto now but what we are going to harvest today is something bad :)
- A Linux box (I'm using Kali Linux)
- theharvester program (already available in Kali Linux)
OK stop talking and start doing.
Fire up a terminal in your kali box and type this command:
theharvester -d hotmail.com -l 50 -b google
In a small amount of time you'll see your terminal flooded with 200 hotmail.com email address. What does this command mean?
theharvester is the tool name that we are using
-d <domain_name> specifies the domain (or website) who's email addresses we're looking for, in our case it was hotmail.com
-l <number> specifies the number of results that we want in the output, I limited it to 50
-b <source> specifies the source on which to look for email addresses, I specified google as the source
Besides google we can specify any of the follow as source:
google, googleCSE, bing, bingapi, pgp, linkedin, google-profiles, people123, jigsaw, twitter, googleplus, all
Here the last entry all means look in every available source.
Let's say you wanted to look in every available source they you should specify the following command:
theharvester -d hotmail.com -b all
-f is another great flag which can be utilized to save the output in case we want to SPAM them later (just kidding) or for other reasons (I'm thinking positive). -f flag saves the result in html or xml format. Let's do just that:
theharvester -d gmail.com -l 50 -b google -f emailaddresses.html
here -f flag is followed by the location where we want to store the file and the name of file, in our case we stored it in our pwd (present working directory) with the name emailaddresses.html.
Above picture shows an html output generated by harvester.
That's it for this tutorial hope to see you next time!
More info
- Pentest Tools Free
- Hacking Tools Download
- Pentest Tools Alternative
- Bluetooth Hacking Tools Kali
- Hack Tools For Ubuntu
- Hacker Tools
- Hacking Tools Software
- Pentest Tools Url Fuzzer
- Hack Rom Tools
- Pentest Tools
- Hack Tools For Windows
- Hacker Tools Free
- Hack Tools
- Best Pentesting Tools 2018
- Hacking Tools For Windows
- How To Install Pentest Tools In Ubuntu
- Hackrf Tools
- Tools Used For Hacking
- Hacker Tools Apk Download
- Hacking Tools For Windows Free Download
- Tools Used For Hacking
- Hack Tools For Ubuntu
- Hack Tools Github
- Hacking Tools Github
- Physical Pentest Tools
- Blackhat Hacker Tools
- Hackrf Tools
- Pentest Tools Android
- Pentest Tools For Android
- Hack Tools Mac
- Pentest Tools Tcp Port Scanner
- Hacker Tools For Windows
- Hacking Tools For Windows
- Hacking Tools For Beginners
- Android Hack Tools Github
- Pentest Tools For Windows
- Hacker Tools Apk Download
- Hacking Tools Online
- Nsa Hacker Tools
- Hack Tools Online
- Best Hacking Tools 2020
- Hacking Tools 2020
- Hacker Search Tools
- Hacking Tools And Software
- Pentest Tools Subdomain
- Hack Tools For Ubuntu
- New Hacker Tools
- Pentest Tools Subdomain
- Termux Hacking Tools 2019
- Pentest Tools Website
- Pentest Tools Android
- Hacker Search Tools
- Android Hack Tools Github
- Hacker Tools Apk
Why Receipt Notifications Increase Security In Signal
Signal, and especially its state update protocol, the Double Ratchet algorithm, are widely known for significantly increasing security for instant messaging. While most users first see the end-to-end security induced by employing Signal in messaging apps, the properties achieved due to ratcheting go far beyond protecting communication against (active) attackers on the wire. Due to updating the local device secrets via the Double Ratchet algorithm, the protocol ensures that attackers, who temporarily obtain a device's local storage (on which Signal runs), only compromise confidentiality of parts of the communications with this device. Thus, the leakage of local secrets from a device only affects security of a short frame of communication. The exact duration of compromise depends on the messaging pattern among the communicating parties (i.e., who sends and receives when), as the state update is conducted during the sending and receiving of payload messages.
The Double Ratchet
The Double Ratchet algorithm consists of two different update mechanisms: the symmetric ratchet and the asymmetric ratchet. The former updates symmetric key material by hashing and then overwriting it with the hash output (i.e., k:=H(k)). Thus, an attacker, obtaining key material can only predict future versions of the state but, due to the one-wayness of the hash function, cannot recover past states. The asymmetric ratchet consists of Diffie-Hellman key exchanges (DHKE). If, during the communication, party A receives a new DH share gb as part of a message from the communication partner B, then A samples a new DH exponent a and responds with the respective DH share ga in the next sent message. On receipt of this DH share, B will again sample a new DH exponent b' and attach the DH share gb' to the next message to A. With every new DH share, a new DHKE gab is computed among A and B and mixed into the key material (i.e., k:=H(k,gab)). For clarity, I leave out a lot of details and accuracy. As new DH shares ga and gb are generated from randomly sampled DH exponents a and b, and the computation of gab is hard if neither a nor b are known, the key material recovers from an exposure of the local secrets to an attacker after a new value gab was freshly established and mixed into it. Summing up this mechanism, if an attacker obtains the local state of a Signal client, then this attacker cannot recover any previously received message (if the message itself was not contained in the local state), nor can it read messages that are sent after a new gab was established and mixed into the state. The latter case happens with every full round-trip among A and B (i.e., A receives from B, A sends to B, and A receives again from B).Research on Ratcheting
During the last two years, the Signal protocol inspired the academic research community: First, a formal security proof of Signal was conducted [1] and then ratcheting was formalized as a generic primitive (independent of Signal) [2,3,4]. This formalization includes security definitions that are derived via 1. defining an attacker, 2. requiring security unless it is obvious that security cannot be reached. Protocols, meeting this optimal notion of security, were less performant than the Double Ratchet algorithm [3,4]. However, it became evident that the Double Ratchet algorithm is not as secure as it could be (e.g., recovery from exposure could be achieved quicker than after a full round-trip; see, e.g., Appendix G of our paper [3]). Afterwards, protocols (for slightly weakened security notions) were proposed that are similarly performant as Signal but also a bit more secure [5,6,7].Protecting Acknowledgments ...
In our analysis of instant messaging group chats [8] two years ago (blog posts: [9,10]), we found out that none of the group chat protocols (Signal, WhatsApp, Threema) actually achieves real recovery from an exposure (thus the asymmetric ratchet is not really effective in groups; a good motivation for the MLS project) and that receipt acknowledgments were not integrity protected in Signal nor WhatsApp. The latter issue allowed an attacker to drop payload messages in transmission and forge receipt acknowledgments to the sender such that the sender falsely thinks the message was received. Signal quickly reacted on our report by treating acknowledgments as normal payload messages: they are now authenticated(-encrypted) using the Double Ratchet algorithm.... Supports Asymmetric Ratchet
Two years after our analysis, I recently looked into the Signal code again. For a training on ratcheting I wanted to create an exercise for which the lines in the code should be found that execute the symmetric and the asymmetric ratchet respectively. Somehow I observed that the pure symmetric ratchet (only updates via hash functions) was nearly never executed (especially not when I expected it) when lively debugging the app but almost always new DH shares were sent or received. I realized that, due to encrypting the receipt acknowledgments now, the app always conducts full round-trips with every payload message. In order to observe the symmetric ratchet, I needed to temporarily turn on the flight mode on my phone such that acknowledgments are not immediately returned. |
| Conceptual depiction of Double Ratchet in Signal now (acknowledgments encrypted). The asymmetric ratchet fully updates the local secrets after an acknowledgment for a message is received. |
Consequently, Signal conducts a full DHKE on every sent payload message (in case the receiving device is not offline) and mixes the result into the state. However, a new DH exponent is always already sampled on the previous receipt (see sketch of protocol above). Thus, the exponent for computing a DHKE maybe remained in the local device state for a while. In order to fully update the state's key material, two round-trips must be initiated by sending two payload messages and receiving the resulting two acknowledgments. Please note that not only the mandatory receipt acknowledgments are encrypted but also notifications on typing and reading a message.
If you didn't understand exactly what that means, here a tl;dr: If an attacker obtains your local device state, then with Signal all previous messages stay secure and (if the attacker does not immediately use these secrets to actively manipulate future conversations) all future messages are secure after you wrote two messages (and received receipt acknowledgments) in all of your conversations. Even though this is very (in practice certainly sufficiently) secure, recent protocols provide stronger security (as mentioned above) and it remains an interesting research goal to increase their performance.
[1] https://eprint.iacr.org/2016/1013.pdf
[2] https://eprint.iacr.org/2016/1028.pdf
[3] https://eprint.iacr.org/2018/296.pdf
[4] https://eprint.iacr.org/2018/553.pdf
[5] https://eprint.iacr.org/2018/889.pdf
[6] https://eprint.iacr.org/2018/954.pdf
[7] https://eprint.iacr.org/2018/1037.pdf
[8] https://eprint.iacr.org/2017/713.pdf
[9] https://web-in-security.blogspot.com/2017/07/insecurities-of-whatsapps-signals-and.html
[10] https://web-in-security.blogspot.com/2018/01/group-instant-messaging-why-baming.html
More info
- Hack App
- Pentest Tools Github
- Pentest Tools Alternative
- Blackhat Hacker Tools
- Hack Tools Online
- Hacking Tools For Games
- Pentest Tools
- Pentest Tools Kali Linux
- Tools Used For Hacking
- Pentest Tools Windows
- Computer Hacker
- Tools 4 Hack
- Hacker
- Pentest Box Tools Download
- Hacking Tools For Games
- Hacking Tools For Mac
- Best Hacking Tools 2019
- Hacking Tools Download
- Game Hacking
- Wifi Hacker Tools For Windows
- Hack Tools
- Pentest Tools Alternative
- Hack Tools For Windows
- Hackers Toolbox
- How To Install Pentest Tools In Ubuntu
- Hack App
- Hacking Tools Windows
- Hack Tools For Games
- Pentest Automation Tools
- Ethical Hacker Tools
- Hack Tools
- Tools For Hacker
- Hacking Tools Software
- Physical Pentest Tools
- Hack Tool Apk No Root
- Hack Tools For Pc
- Hacking Tools Hardware
- Wifi Hacker Tools For Windows
- Hacking Tools For Games
- Pentest Tools Find Subdomains
- Pentest Tools Port Scanner
- Hacking Apps
- Hacker Tools Online
- Pentest Automation Tools
- Pentest Automation Tools
- Hacker Tools For Pc
- Nsa Hack Tools Download
- Hacking Tools For Windows 7
- Hacking Tools Online
- Beginner Hacker Tools
- Hacker Tool Kit
- Tools 4 Hack
- Hacking Tools 2019
- Hacker Tools
- Pentest Box Tools Download
- Nsa Hacker Tools
- Usb Pentest Tools
- Hack Tool Apk No Root
- Hacking Tools For Windows Free Download
- Hack Tools Github
- Pentest Tools Linux
- Hacking Tools For Windows 7
- Underground Hacker Sites
- Hacking Tools Usb
- Hacking Tools Download
- Tools 4 Hack
- Hacker Search Tools
domingo, 4 de junho de 2023
RenApp: The Ultimate File Renaming App

- Rename files to a common name.
- Rename files of different extensions to a common name in one shot
- Remove backup files from folder and subfolders.
- Pentest Tools Framework
- Pentest Tools Apk
- Hacking Tools For Windows Free Download
- Hack Tools 2019
- World No 1 Hacker Software
- Pentest Tools Url Fuzzer
- Computer Hacker
- Install Pentest Tools Ubuntu
- Hack And Tools
- Pentest Tools Open Source
- Hacking Tools For Windows 7
- How To Install Pentest Tools In Ubuntu
- Physical Pentest Tools
- Pentest Tools For Android
- Pentest Tools Find Subdomains
- Pentest Tools Website Vulnerability
- Android Hack Tools Github
- Hacking App
- Pentest Tools Website
- Hacking Tools Pc
- Hack Tools For Windows
- Hacking Tools
- Hack Tools For Games
- What Are Hacking Tools
- Hacker Tools
- Tools Used For Hacking
- Hacker Tools Windows
- Hack Tools For Ubuntu
- Hacks And Tools
- Tools 4 Hack
- Hacker Tools Free Download
- Pentest Tools Find Subdomains
- Hackers Toolbox
- Free Pentest Tools For Windows
- Hacking Tools For Beginners
- Tools For Hacker
- Pentest Tools For Mac
- Pentest Tools Bluekeep
- Hack Tools For Ubuntu
- Pentest Reporting Tools
- Easy Hack Tools
- Hacking App
- Tools Used For Hacking
- Hacker Tools Apk
- Growth Hacker Tools
- Hacker Security Tools
- Hak5 Tools
- Nsa Hack Tools Download
- Hacker Tools For Ios
- Hacking Tools For Windows 7
- Hacking Tools Mac
- Pentest Tools Subdomain
- Pentest Tools Website Vulnerability
- Hacking Tools Pc
- Hack Rom Tools
- Pentest Tools Kali Linux
- Hacker Tools
- Hacking Tools For Windows
- Hacker
- What Is Hacking Tools
- Hacking Tools
- Hack Tools For Ubuntu
- Growth Hacker Tools
- Kik Hack Tools
- Pentest Tools
- Hacks And Tools
- Pentest Tools Tcp Port Scanner
- Physical Pentest Tools
- Hacker Tools For Windows
- Hacker Tools For Ios
- Hacker
- Pentest Tools Website
- New Hack Tools
- Hacker Tools For Mac
- Hacking Tools Hardware
- Termux Hacking Tools 2019
- Pentest Tools For Android
- Hacker Tools For Pc
- Usb Pentest Tools
- Hacker Techniques Tools And Incident Handling
- Hacker Tools Apk
- Android Hack Tools Github
- Pentest Tools Download
- Hak5 Tools
- Hacking Tools For Pc
- Hacking Tools Online
- World No 1 Hacker Software
- Nsa Hack Tools Download
- Hacker Tools Mac
- Hacking Tools Pc
- Hacker Tools Hardware
- Hacking Tools Pc
- Pentest Tools For Ubuntu
- Nsa Hacker Tools
- Pentest Tools Tcp Port Scanner
- Pentest Tools Open Source
- Hack Tool Apk No Root
- Blackhat Hacker Tools
- Hack Tools Download
- Hacker Tools List
- Physical Pentest Tools
- Hacker Hardware Tools
- Hack Tools For Mac
- Pentest Tools Tcp Port Scanner
- Pentest Tools
- Hacking Tools Name
- Pentest Tools Alternative
- Pentest Tools Port Scanner
- Blackhat Hacker Tools
- Pentest Tools Port Scanner
- Computer Hacker
- Pentest Tools Tcp Port Scanner
- How To Install Pentest Tools In Ubuntu
- Hacking Tools Kit
- Hacking Tools 2019
- Hack Tools
- Hacking Tools And Software
- Pentest Tools Website Vulnerability
- Best Hacking Tools 2020
- Pentest Tools For Ubuntu
- Hacking Tools For Beginners
- Termux Hacking Tools 2019
- Pentest Tools Free
- Hacker
- Hack Tools Mac
- Bluetooth Hacking Tools Kali
- Hacking Tools 2019
- Hacking App
- Pentest Tools Online
- Usb Pentest Tools
- Tools For Hacker
- Hack Rom Tools
- Hacking Tools Pc
- Pentest Tools Online
- Hackrf Tools
- Hack Tools Pc
- Kik Hack Tools
- Pentest Tools Free
- Hacking App
- Hacking Tools Kit
- Hacking Tools For Games
- Pentest Tools Port Scanner
- World No 1 Hacker Software
- Hacker Tools Linux
- Free Pentest Tools For Windows
- Hacker Tools Linux
- Pentest Tools Windows
- Pentest Tools Github
- Free Pentest Tools For Windows
- Pentest Tools Port Scanner
- Hacker Search Tools
- Pentest Tools Github
Automating REST Security Part 1: Challenges
Although REST has been a dominant choice for API design for the last decade, there is still little dedicated security research on the subject of REST APIs. The popularity of REST contrasts with a surprisingly small number of systematic approaches to REST security analysis. This contrast is also reflected in the low availability of analysis tools and best security practices that services may use to check if their API is secure.
In this blog series, we try to find reasons for this situation and what we can do about it. In particular, we will investigate why general REST security assessments seem more complicated than other API architectures. We will likewise discuss how we may still find systematic approaches for REST API analysis despite REST's challenges. Furthermore, we will present REST-Attacker, a novel analysis tool designed for automated REST API security testing. In this context, we will examine some of the practical tests provided by REST-Attacker and explore the test results for a small selection of real-world API implementations.
Author
Christoph Heine
Overview
- Automating REST Security Part 1: Challenges
- Automating REST Security Part 2: Tool-based Analysis with REST-Attacker
- Automating REST Security Part 3: Practical Tests for Real-World APIs
Understanding the Problem with REST
When evaluating network components and software security, we often rely on specifications for how things should work. For example, central authorities like the IETF standardize many popular web technologies such as HTTP, TLS or DNS. API architectures and designs can also be standardized. Examples of these technologies are SOAP and the more recent GraphQL language specification. Standardization of web standards usually influences their security. Drafting may involve a public review process before publication. This process can identify security flaws or allow the formulation of official implementation and usage best practices. Best practices are great for security research as a specification presents clear guidelines on how an implementation should behave and why.
The situation for REST is slightly different. First of all, REST is not a standard in the sense that there is no technical specification for its implementation. Instead, REST is an architecture style which is more comparable to a collection of paradigms (client-server architecture, statelessness, cacheability, uniform interface, layering, and code-on-demand). Notably, REST has no strict dependency on other web technologies. It only defines how developers should use components but not what components they should use. This paradigm makes REST very flexible as developers are not limited to any particular protocol, library, or data structure.
Furthermore, no central authority could define rules or implementation guidelines. Roy Fielding created the original definition of REST as a design template for the HTTP/1.1 standard in 2000. It is the closest document resembling a standard. However, the document merely explains the REST paradigms and does not focus on security implications.
The flexibility of the REST architecture is probably one of the primary reasons why security research can be challenging. If every implementation is potentially different, how are we supposed to create common best practices, let alone test them consistently across hundreds of APIs? Fortunately for us, not every API tries to reinvent the wheel entirely. In practice, there are a lot of similarities between implementations that may be used to our advantage.
Generalizing REST Security
The most glaring similarity between REST API implementations is that most, if not all, are based on HTTP. If you have worked with REST APIs before, this statement might sound like stating the obvious. However, remember that REST technically does not require a specific protocol. Assuming that every REST API uses HTTP, we can use it as a starting point for a generalization of REST API security. Knowing that we mainly deal with HTTP is also advantageous because HTTP - unlike REST - is standardized. Although HTTP is still complex, it gives us a general idea of what we can expect.
Another observation is that REST API implementations reuse several standardized components in HTTP for API communication. Control parameters and actions in an API request are mapped to components in a generic HTTP request. For example, a resource that an API request operates on, is specified via the HTTP URL. Actions or operations on the said resource are identified and mapped to HTTP methods defined by the HTTP standard, usually GET, POST, DELETE, PUT, and PATCH. API operations retain their intended action from HTTP, i.e., GET retrieves a resource, DELETE removes a resource, and so on. In REST API documentation, we can often find a description of available API endpoints using HTTP "language":
Since the URL and the HTTP method are sufficient to build a basic HTTP request, we can potentially create an API requests if we know a list of REST endpoints. In practice, the construction of such requests can be more complicated because the API may have additional parameter requirements for their requests, e.g., query, header, or body content. Another problem is finding valid IDs of resources can be difficult. Interestingly, we can infer each endpoint's action based on the HTTP method, even without any context-specific knowledge about the API.
We can also find components taken from the HTTP standard in the API response. The requested operation's success or failure is usually indicated using HTTP status codes. They retain their meaning when used in REST APIs. For example, a 200 status code indicates success, while a 401 status code signifies missing authorization (in the preceding API request). This behavior again can be inferred without knowing the exact purpose of the API.
Another factor that influences REST's complexity is its statelessness paradigm. Essentially, statelessness requires that the server does not keep a session between individual requests. As a result, every client request must be self-contained, so multi-message operations are out of the picture. It also effectively limits interaction with the API to two HTTP messages: client request and server response. Not only does this make API communication easier to comprehend, but it also makes testing more manageable since we don't have to worry as much about side effects or keeping track of an operations state.
Implementing access control mechanisms can be more complicated, but we can still find general similarities. While REST does not require any particular authentication or authorization methods, the variety of approaches found in practice is small. REST API implementations usually implement a selection of these methods:
- HTTP Basic Authentication (user authentication)
- API keys (client authentication)
- OAuth2 (authorization)
Two of these methods, OAuth2 and HTTP Basic Authentication, are standardized, while API keys are relatively simple to handle. Therefore, we can generalize access control to some degree. However, access control can be one of the trickier parts of API communication as there may be a lot of API-specific configurations. For example, OAuth2 authorization allows the API to define multiple access levels that may be required to access different resources or operations. How access control data is delivered in the HTTP message may also depend on the API, e.g., by requiring encoding of credentials or passing them in a specified location of the HTTP message (e.g. header, query, or body).
Finding a Systematic Approach for REST API Analysis
So far, we've only discussed theoretical approaches scatching a generic REST API analysis. For implementing an automated analysis tool, we need to adopt the hints that we used for our theoretical API analyses to the tool. For example, the tool would need to know which API endpoints exist to create API requests on its own.
The OpenAPI specification is a popular REST API description format that can be used for such purpose. An OpenAPI file contains a machine-readable definition (as JSON or YAML) of an API's interface. Basic descriptions include the definition of the API endpoints, but can optionally contain much more content and other types of useful information. For example, an endpoint definition may include a list of required parameters for requests, possible response codes and content schemas of API responses. The OpenAPI can even describe security requirements that define what types of access control methods are used.
{ "openapi": "3.1.0", "info": { "title": "Example API", "version": "1.0" }, "servers": [ { "url": "http://api.example.com" } ], "paths": { "/user/info": { "get": { "description": "Returns information about a user.", "parameters": [ { "name": "id", "in": "query", "description": "User ID", "required": true } ], "responses": { "200": { "description": "User information.", "content": { "application/json": { "schema": { "type": "object", "items": { "$ref": "#/components/schemas/user_info" } } } } } } } } }, "security": [ { "api_key": [] } ] } As you can see from the example above, OpenAPI files allow tools to both understand the API and use the available information to create valid API requests. Furthermore, the definition can give insight into the expected behavior of the API, e.g., by checking the response definitions. These properties make the OpenAPI format another standard on which we can rely. Essentially, a tool that can parse and understand OpenAPI can understand any generic API. With the help of OpenAPI, tools can create and execute tests for APIs automatically. Of course, the ability of tools to derive tests still depends on how much information an OpenAPI file provides. However, wherever possible, automation can potentially eliminate a lot of manual work in the testing process.
Conclusion
When we consider the similarities between REST APIs and OpenAPI descriptions, we can see that there is potential for analyzing REST security with tools. Our next blog post discusses how such an implementation would look like. We will discuss REST-Attacker, our tool for analyzing REST APIs.
Further Reading
The feasibility of tool-based REST analysis has also been discussed in scientific papers. If you want to know more about the topic, you can start here:
- Atlidakis et al., Checking Security Properties of Cloud Service REST APIs (DOI Link)
- Lo et al., On the Need for a General REST-Security Framework (DOI Link)
- Nguyen et al., On the Security Expressiveness of REST-Based API Definition Languages (DOI Link)
Acknowledgement
The REST-Attacker project was developed as part of a master's thesis at the Chair of Network & Data Security of the Ruhr University Bochum. I would like to thank my supervisors Louis Jannett, Christian Mainka, Vladislav Mladenov, and Jörg Schwenk for their continued support during the development and review of the project.
Related word- Hacking Tools For Mac
- Easy Hack Tools
- Top Pentest Tools
- Hacker Search Tools
- Hack And Tools
- Hacking Tools For Pc
- Hacker Tools Windows
- Hacker Tools Windows
- Hacker Tools For Pc
- Hacking Apps
- Tools Used For Hacking
- Hacker Techniques Tools And Incident Handling
- What Is Hacking Tools
- Hacker Tools Apk Download
- Game Hacking
- Hacker Tools Mac
- Hack Tools For Games
- Black Hat Hacker Tools
- Hack Apps
- Hack Tools For Windows
- Hack Tool Apk
- Hack Tools Online
- Hacker Search Tools
- Growth Hacker Tools
- New Hacker Tools
- Hacking Tools For Pc
- Hack Rom Tools
- Hacking Tools Free Download
- Hacking Apps
- Nsa Hacker Tools
- Pentest Tools Kali Linux
- Pentest Tools For Windows
- Hack Tools For Games
- Pentest Tools Linux
- Top Pentest Tools
- Hacker Tools Windows
- Pentest Tools Url Fuzzer
- Blackhat Hacker Tools
- Pentest Tools For Ubuntu
- Hacker Tools For Ios
- Hacking Tools Usb
- Hacker Tools Free
- Pentest Tools Framework
- Pentest Tools Website
- Hacking Tools Hardware
- Hack Tools For Ubuntu
- Hacks And Tools
- Hacking Tools Kit
- Hacker Tools Windows
- How To Hack
- Hacking Tools For Beginners
- Install Pentest Tools Ubuntu
- Hacking Tools Mac
- Hackrf Tools
- Hacking Tools For Windows
- Computer Hacker
- Hack Tools Github
- Pentest Tools For Mac
- Github Hacking Tools
- Hacker Tools For Ios
- Tools For Hacker
- Hacker Tools Free
- World No 1 Hacker Software
- Hacking Tools Download
- Hacker Tools Hardware
- Hacker Tools Windows
- Pentest Tools Apk
- Github Hacking Tools
- Hack Tool Apk
- Hack Tools Pc
- Pentest Recon Tools
- Hacking Tools For Games
- Hacker Tools Apk
- Pentest Tools Linux
- Wifi Hacker Tools For Windows
- Usb Pentest Tools
- World No 1 Hacker Software
- Hackrf Tools
- Pentest Box Tools Download
- Hacking Tools For Windows 7
- Hack Tool Apk
- Hacking Tools Online
- Pentest Recon Tools
- Hacker Security Tools
- Hack Tools 2019
- Tools Used For Hacking
- Physical Pentest Tools
- Pentest Tools Alternative
- New Hack Tools
- Pentest Tools For Windows
- Hacker
- Hacker Tools Software
- Beginner Hacker Tools
- Ethical Hacker Tools
- Hacking Tools Online
- Hack App
- Install Pentest Tools Ubuntu
- Hacker Hardware Tools
- How To Make Hacking Tools
- Hacker
- Hack Tool Apk
- Best Hacking Tools 2019
- Hacker Tools 2020
- Pentest Tools Windows
- Hacking Tools
- Growth Hacker Tools
- Tools 4 Hack
- Beginner Hacker Tools
- Tools 4 Hack
- Hack Tools For Mac
- Hacking Tools 2019
- Hacker Tools Apk Download
- Pentest Tools For Android
- Hacker Tools Apk
- Hacking Tools Free Download
- Tools Used For Hacking
- New Hack Tools
- Hacking Tools Name
- Underground Hacker Sites
- Nsa Hack Tools Download
- Free Pentest Tools For Windows
- Hacker
- Hacking Tools Github
- What Are Hacking Tools
- Hacking Tools
- Hacking Tools Usb
- Hack Tools For Games
- Best Pentesting Tools 2018
- Pentest Tools Github
- Termux Hacking Tools 2019